Search Results cyber — E-International Relations.
Cyber Essays is your one-stop source for free, high-quality term papers, essays, and reports on all sorts fo subjects. Please use either the paper categories or our database search to quickly and easily find the paper you need. Also, check out our forums where you can talk to people about whatever is on your mind as well as share term papers.
Search. You can search our site by entering a search query in the box below. If you can't find what you are looking for, try making your search queries shorter or less specific.

COURSE OVERVIEW. Learn from a specialist team of research-active academics who work at the forefront of the field; Access a wide range of specialist software and tools including a dedicated Cyber Security and Forensics laboratory in a state-of-the-art new development (from 2020).

Our depot contains over 15,000 free essays. Read our examples to help you be a better writer and earn better grades!
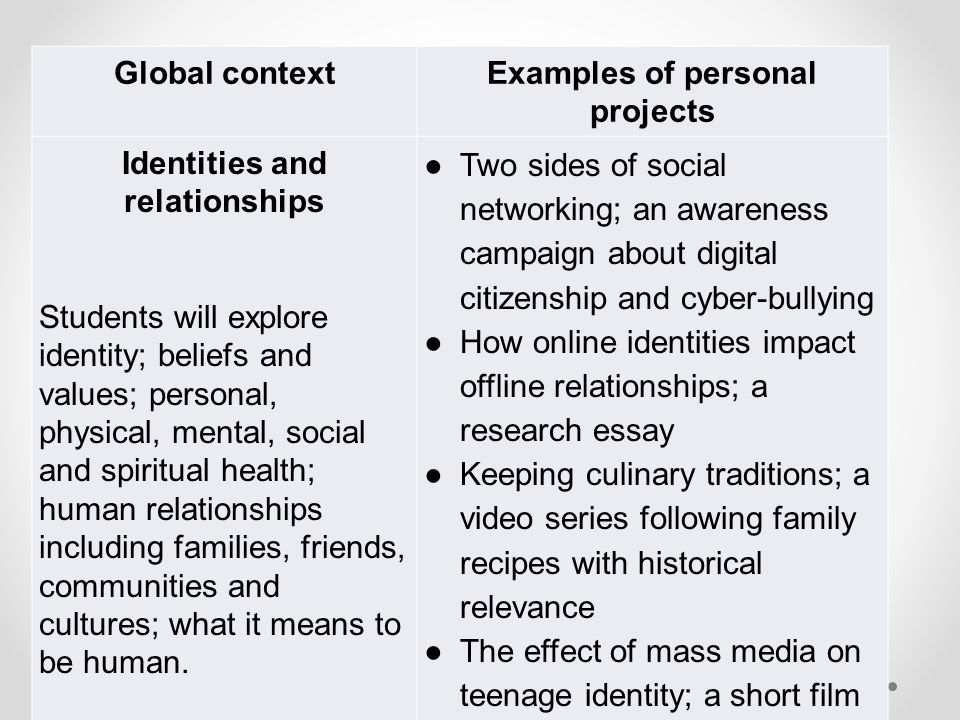
The cyber bully is the person with the problem, not you. Being cyber bullied is also like having your worst nightmare following you home. The number of teen suicide due to the cyber bullying is increasing day by day. Second try to view cyber bullying from a different perspective. The cyber bully is an unhappy, frustrated person who wants to.
Disclaimer: This work has been submitted by a student. This is not an example of the work produced by our Essay Writing Service.You can view samples of our professional work here. Any opinions, findings, conclusions or recommendations expressed in this material are those of the authors and do not necessarily reflect the views of UK Essays.
Free Essays on Cyber Revolution. Get help with your writing. 1 through 30.
Forensics and Cyber Crime essays and term papers available at echeat.com, the largest free essay community.

Free cyber crime papers, essays, and research papers. My Account. Your search. Better Essays. Stronger Essays. Powerful Essays. Term Papers. Research Papers. Cyber Criminals: Cyber-Crime and Cyberstalking - People want to feel safe. If someone owns a precious object it is stored in a safe hidden in their house. To further protect a house the front doors have handle locks and dead-bolts. To.
Bing’s importance in the information landscape of the U.S. shouldn’t be overlooked. While its share of the search market in the U.S. might be dwarfed by that of Google, it has steadily increased over the past ten years. Bing’s partnerships with Yahoo, AOL, DuckDuckGo, and Apple mean that even users who don’t use Bing as their default search engine or go directly to its home.
This timeline records significant cyber incidents since 2006. We focus on cyber attacks on government agencies, defense and high tech companies, or economic crimes with losses of more than a million dollars. Download the Full Incidents List Below is a summary of incidents from over the last year. For the full list, click the download link above.

The Cyber Manhunt Cyber Manhunt, also known as Human Flesh Search or Internet Mass Hunting is primarily a Chinese Internet phenomenon of massive searching in which numerous Internet users participate to filter the search results and assists users in clarifying their search request. It literally means to uncover the true identity of a particular.

Essay on The Cyber Manhunt; Essay on The Cyber Manhunt. 883 Words 4 Pages. Show More. The Cyber Manhunt Cyber Manhunt, also known as Human Flesh Search or Internet Mass Hunting is primarily a Chinese Internet phenomenon of massive searching in which numerous Internet users participate to filter the search results and assists users in clarifying their search request. It literally means to.