A1.1 Homework 1 Answers - Cambridge Essentials.
A2.2 Homework Answers 1 a The number that goes into a function machine is called the input. b The output is the number that comes out of the function machine. c What happens to the number as it moves through the machine is called the function.
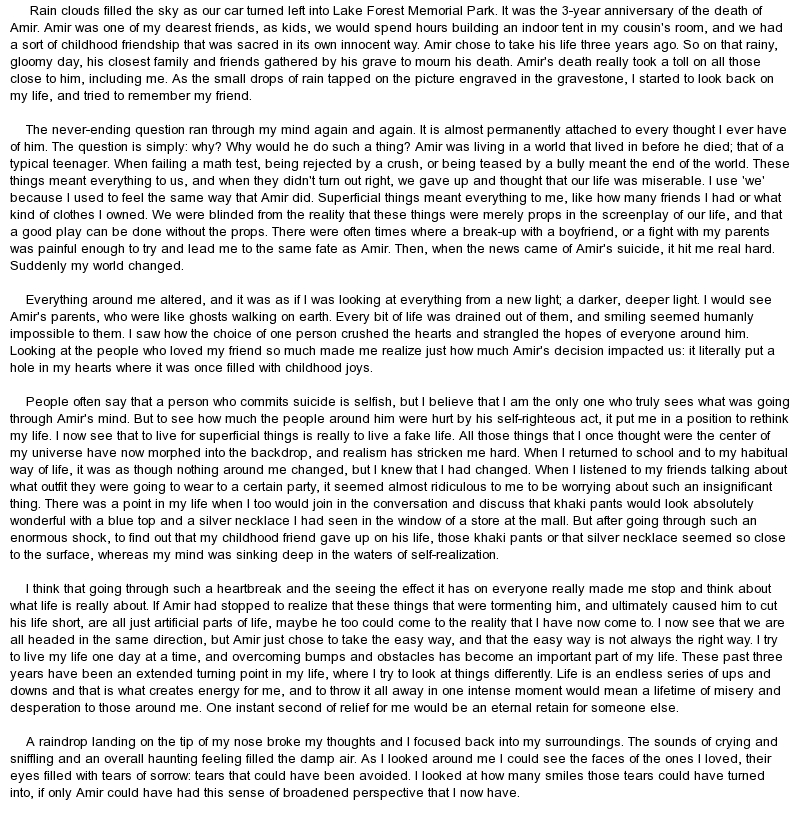
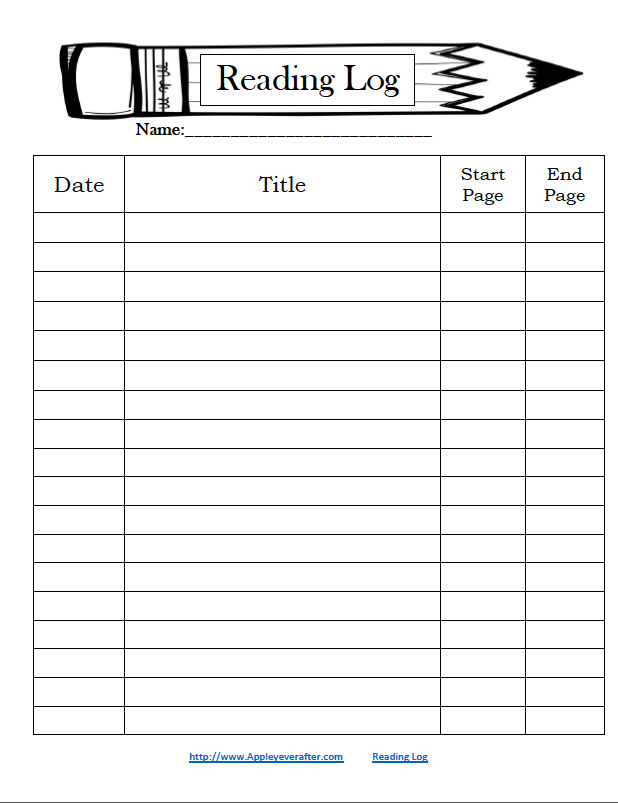
Homework, or a homework assignment, is a set of tasks assigned to students by their teachers to be completed outside the class. Common homework assignments may include required reading, a writing or typing project, mathematical exercises to be completed, information to be reviewed before a test, or other skills to be practiced.

CYBER SECURITY ASSIGNMENT HELP. As technology evolves and the world adopts internet connectivity and communication in every aspect of life and cyber-space, attacks have transformed from the normal theft of office documents to cyber-attacks. In 2019, more than 4.1 billion records were exposed as a result of cyber-security attacks.
Want to pay someone to do your programming homework and get a better grade? We offer professional programming assignment help services. We are the cheapest programming homework writing service. Make your order for customized programming assignment solutions now.
CPM Education Program proudly works to offer more and better math education to more students.

Welcome to MORE! Second Edition - Cyber Homework and Online Resources! All the online materials follow the syllabus and language of MORE! Second Edition and provide further practice in key areas of English language and culture.

Question(s) asked are for you to think about on your own and need not be turned in with the homework.) 4.0: Since we're using JavaCC, a recursive descent parser, take special note of semantic actions in the sections to come. 4.1: The values we'll be returning from semantic actions will be parts of abstract syntax trees. Think back on the first.

SM221 Multivariable Calculus with Vectors. Access to Homework Solutions Restricted to Students in my Classes. Vector Calculus Summaries (2 Versions): Version 1 Version 2.
MAKE YOUR ACADEMIC LIFE EASY BY AVAILING CPM HOMEWORK HELP Services FROM TRUSTED CPM HELPERS OF Chicago. CPM homework tasks are incredibly complicated and are not possible for every student to finish it in a given time. They need to have great mathematical knowledge regarding their formulas and calculations. Therefore, to resolve this obstacle.
Question: Cyber Exploration Laboratory Experiment 4.1 Objective To The Effect Of Pole And Zero Location Upon The Time Evaluate Response Of First- And Second-order Systems Required Software Packages MATLAB. Simulink, And The Control System Prelab 1. Given The Transfer Function G (s) Evaluate Settling Time And Rise Time For A S The Following Values Of A: 1, 2.
Solve calculus and algebra problems online with Cymath math problem solver with steps to show your work. Get the Cymath math solving app on your smartphone!
St John's C.E. Primary School. Cookie Notice. We use cookies to track usage and improve the website. Click here for more information. I Understand.

Search the world's information, including webpages, images, videos and more. Google has many special features to help you find exactly what you're looking for.